Your Vendor List Reads Like a Breach Report
How third-party vendors became one of your biggest cybersecurity risks, and what IT leaders really need to start focusing on and planning more for.
How confident are you that your vendors are not your next breach?
I’ve seen this play out too many times, vendor sprawl might be the sneakiest security risk in IT. Every SaaS tool, cloud service, or AI platform we bring in quietly pushes the door open wider. But somehow, vendor management still lands with finance or procurement (If you know you know). And look, we’re all obviously focused on making sure our companies have the most cutting-edge access to tech, keeping stakeholders happy is part of the job. But how we do that matters. Paying attention to the vendors you’re onboarding or using matters…
a lot more than you might think.
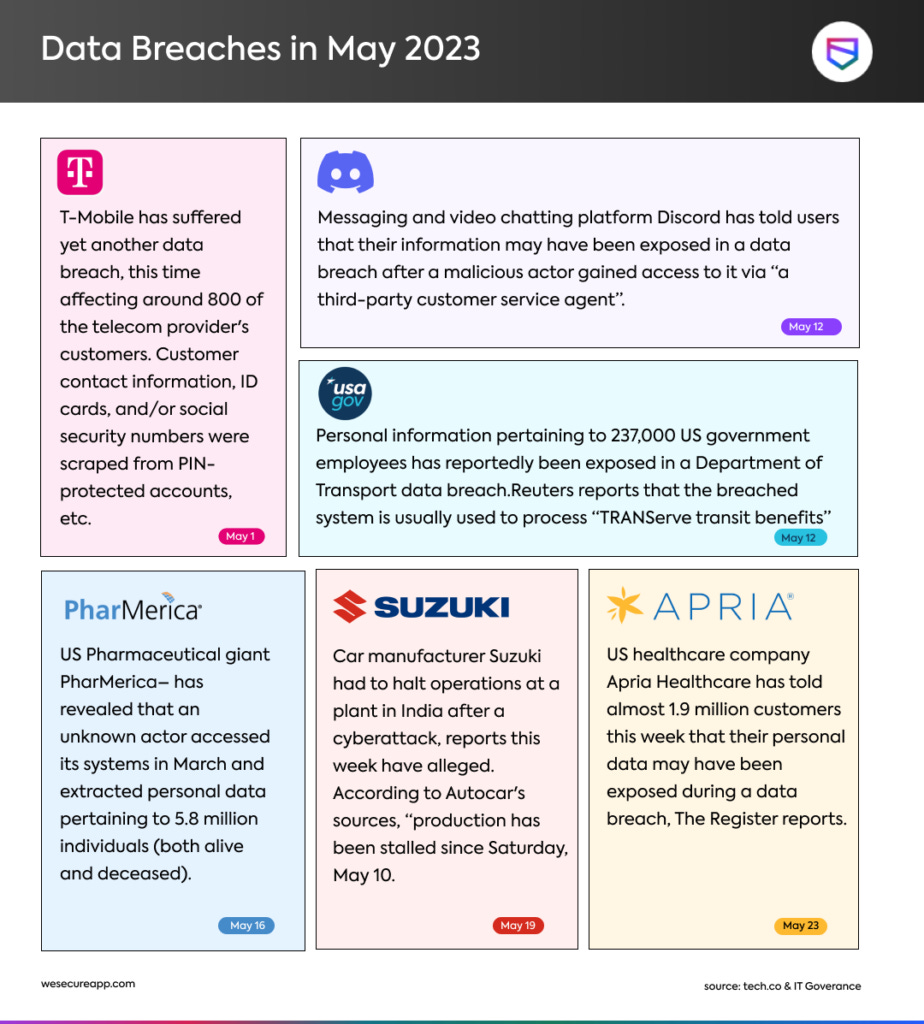
The Breaches Keep Coming, and They All Start Outside
It’s wild, according to the 2023 IBM Cost of a Data Breach Report, just having a third-party involved in a breach raises the cost by 19%. And honestly, I’ve felt that number in real conversations with folks trying to clean up after these hits.
The Okta breach? Kicked off by a third-party vendor. MOVEit? That one hit hundreds of companies! Not because of what they did, but because of supply chain exposure.
And who can forget Target? That massive breach didn’t start with some sophisticated cyber-attack on their core systems, it literally started with an HVAC vendor! Imagine answering to your CISO that a massive, multi-million dollar data breach happened through your HVAC team.
And every time, we frame it like a failure of the perimeter, like someone broke down the door. But that’s not really it. These are failures to control who we’re letting inside in the first place. And once they’re in… it’s too late.
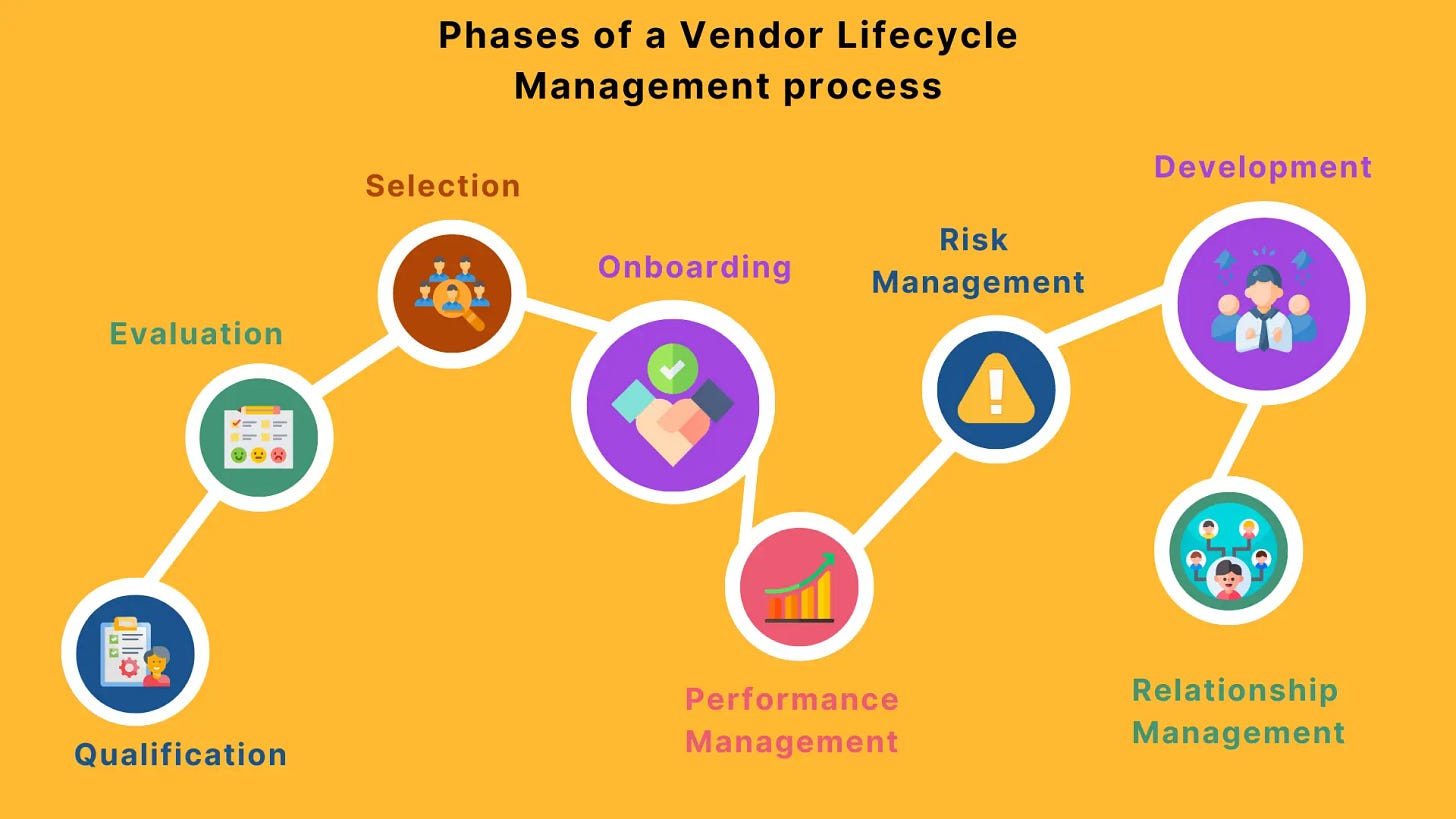
Why IT Leaders Must Own Vendor Management
Vendor management is not procurement's job anymore. Here is why:
Procurement focuses on cost savings but cannot assess technical risk
Compliance reviews paperwork but rarely evaluates exposure
Security owns risk but is often brought in too late to influence decisions
In a previous role, I myself was pulled in after a CRM contract was signed. Only then did we discover the platform stored sensitive customer data offshore, in a country without data privacy protections. We spent weeks untangling that mistake. If IT leadership had owned vendor review from the start, we could have avoided the risk entirely.
The Framework: Actionable Steps to Implement Now
1. Build a Vendor Risk Matrix
Classify vendors by:
Access level (critical systems versus non-production)
Data sensitivity (PII, financial, proprietary)
Breach history or risk profile
2. Require Security Reviews Before Signing
No vendor enters production without IT-led technical evaluation and security review.
3. Design an Exit Strategy at Onboarding
Define offboarding steps immediately, including revoking access, deleting data, and performing a final audit. Assume every vendor relationship ends eventually.
AI Makes This Worse, Fast
Generative AI tools flood the market, increasing vendor onboarding speed. Shadow IT is becoming AI-powered, and your organization may already be leaking sensitive data into tools no one has evaluated.
If you do not adapt your vendor strategy to manage AI risk, you are falling behind.
Key Takeaway
The next breach will not start inside your systems. It will start in the systems you invited without realizing the cost.
Vendor management is security. It is an operational risk. IT leaders must own this process to prevent their company from making the next breach headline.
Reach Out
After collaborating with several leaders in this space, I’m actively joining conversations around this challenge. If you’re an IT or security leader navigating vendor risk and third-party breaches, let’s connect. Drop a comment or message me - I’d love to compare frameworks and approaches.